Indonesia’s e-commerce unicorn Tokopedia made some negative headlines this week. On Friday, a user or group going by the name of “Whysodank” published data of 15 million Tokopedia customers on a hacker site called “Raid Forum”. On the site, Whysodank was looking for programmers who could decrypt the password hash of the Tokopedia accounts.
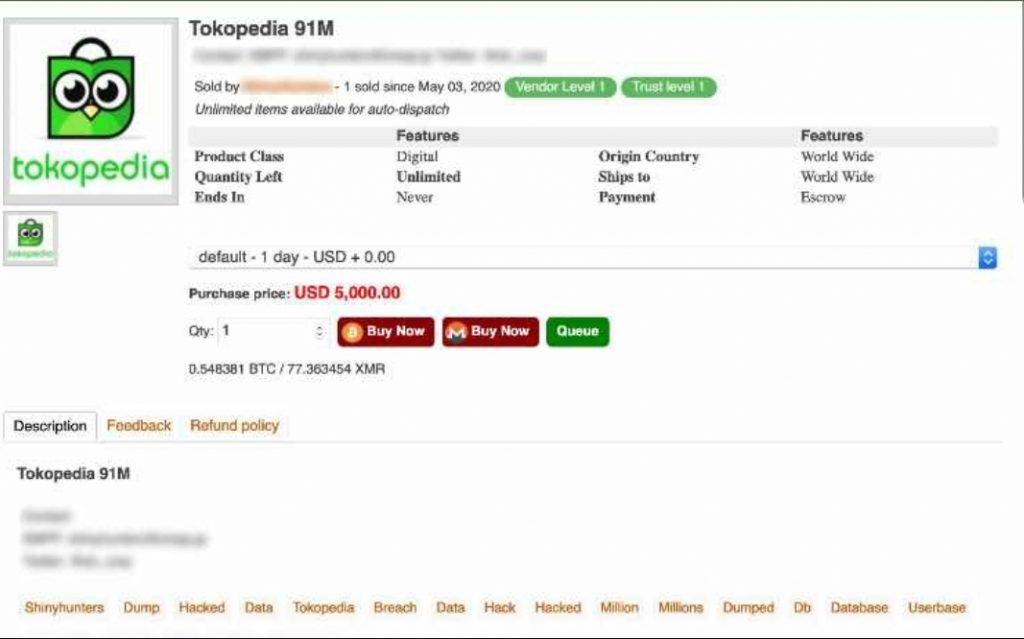
Several users of the forum immediately offered help. On Saturday night, Whysodank declared that he had the data of all 91 million Tokopedia users including names, birth dates, genders, e-mail addresses, and phone numbers. He then sold the data on the dark web site Empire Market for USD 5,000, using the nickname “ShinyHunters”.
The leakage and sale of the data were later published on Twitter by the data breach monitoring firm Under the Breach which immediately provoked the anger of Indonesian netizens.
Responding to the issue, Tokopedia quickly admitted that it discovered an attempt to steal data from its servers, but said that the passwords are still protected and that no payment information was leaked. However, the company said that users should change their passwords to be safe.
Tokopedia was summoned by the IT Ministry and National Cyber and Encryption Agency (BSSN) to discuss the case on Monday. After the meeting, Minister Johnny G. Plate said that users’ financial data is still protected. “Tokopedia told us that the financial information of its customers is safe. Its security system has not been breached, although some data related to names, e-mails and telephones may have been accessed by hackers,” he said in a statement.
Red flag for data protection
This case has drawn a lot of criticism from the public who is horrified that a tech company as big as Tokopedia could lose user data. Although the company said that passwords and financial data are safe, some analysts and researchers believe that it is only a matter of time for hackers to crack those passwords as well.
The founder of Ethical Hacker Indonesia and cybersecurity consultant Teguh Aprianto said that the process of hacking 90 million data sets takes quite some time, so it is questionable why Tokopedia didn’t notice it earlier. “Even though passwords have not been hacked so far, phone numbers and e-mail addresses are sensitive data that is prone to cybercrime,” Aprianto told KrASIA. “Email owners can be targeted for spam and phishing, to steal other account information including credit card and bank details.”
Tokopedia has a bug bounty program, but the firm was criticized by the hacker community and researchers for not implementing a transparent bug bounty process, according to Aprianto. A bug bounty program is a crowdsourcing initiative that rewards individuals for discovering and reporting software bugs. Such a program is common for tech companies as part of their vulnerability management strategy.
Other tech giants with bug bounty programs are Gojek, Grab, and Bukalapak which had its own case of data leakage last year. The companies pay out cash rewards to software security researchers and ethical hackers who report bugs or vulnerabilities that have the potential to be exploited.
Nonetheless, Aprianto believes that Tokopedia does not run the program optimally. “There have been cases where the community reported valid bug findings, but Tokopedia said that these bugs had been found internally, and the reporter did not get a reward,” he said. “The bug fixing process did not finish for months, so we were suspicious whether the bugs had been really found and handled by the company.”
Read this: This company puts all your contacts on the cloud: Q&A with Sansan regional CEO Edward Senju
Budget limitations could be a reason why programs are not implemented properly. “They can be very expensive,” Aprianto said. As a reference, Microsoft recently launched a new Xbox bounty program to reward gamers and security researchers with USD 500 to USD 20,000 for discovering issues. Google offered USD 1.5 million for its Android bug bounty program last year.
Meanwhile in Indonesia, Gojek also has a competitive price for its program. According to Bugcrowd, the firm pays USD 200 to USD 5,000 per bug, depending on how critical the findings are.
A bug bounty is only one strategy and a big company like Tokopedia is likely to have other ways to protect its systems. Even so, the data leak manifests a serious gap in the company’s system compromising user privacy.
Data hacks are a scourge for any tech company. Last year, Bukalapak confirmed an attempted breach, that failed, according to the firm, because it had upgraded its security system.
Responding to the most recent incident, Bukalapak said that it implemented a multi-layered protection system to receive, store, and process user data. “The protection of customer data is our priority, so we continuously improve the security to ensure that it is not being mishandled,” Intan Wibisono, Bukalapak’s head of corporate communications told KrASIA. Other platforms that have had problems with scammers are the travel tech provider Tiket and the O2O platform Kudo (now GrabKios by Kudo).
If tech unicorns like Tokopedia and Bukalapak can be victims of data breaches, other platforms are likely to be an even easier target. Hackers are evidently refining their skills, so that tech platforms, especially those with millions of users, need to raise their game as well, including investing more in security programs, in order to respond to more sophisticated cyber crimes.
Regulator must act firmly
It is also a warning for the government—as the regulator—to be more stringent in protecting public data. Law enforcement must move quickly to investigate cybercrime before the public suffers the consequences of weak data protection.
“The government needs to form an independent investigation team to find out how this leak happened. Sometimes a leak can occur because the government is not strict enough and simply accepts company reports that may not be 100% honest in acknowledging there is a leak in their systems,” Heru Sutadi, executive director of the Indonesia ICT Institute told KrASIA.
For Sutadi, this event will certainly have a big impact, not only for Tokopedia but the entire Indonesian e-commerce industry. “If there is a data breach, the public trust in e-commerce can go down which is troubling for the development of Indonesia’s digital economy,” he said.
Indonesia already has a draft data protection law that was submitted by President Joko Widodo to the House of Representatives in January 2020, but the draft hasn’t formalized into official law yet. One of the main aspects is that data controllers or companies must report leaks to data owners—the consumers—and to the ministry and agencies transparently. Article 68 of the draft law establishes fines of up to IDR 5 billion (USD 330,700) for intentional or unlawful disclose of personal data to other parties.
However, several important aspects are still missing, according to Sutadi. “The draft law does not provide details regarding the obligation to place data centers in Indonesia. It also does not specify the existence of independent institutions to regulate, supervise, and control personal data,” said Sutadi.
Therefore, data laws still need to be tougher. One good example to follow is the General Data Protection Regulation in the European Union, which secures personal data such as names, home and IP addresses, as well as genetic and biometric data. Companies are obligated to protect their customer information and can be severely punished for negligence or privacy violations.
“In Europe, companies can be fined hundreds of thousands or even millions of euro for failing to protect user data. I think Indonesia needs to implement similar regulations to create a deterrent effect for companies,” said Aprianto. “Many consumers are not yet aware of how important it is to keep personal data safe and most likely won’t go and defend their rights in court. Therefore the government must be more proactive in protecting them.”
What to do if your data is leaked?
It is important to be alert to spam and junk messages. Responding to or clicking on links within spam messages is a risk and it may inadvertently install a virus on your computer or expose your address to a data breach. If you are worried about your personal information being leaked in the cyberspace, Aprianto recommends immediate updating of passwords for your e-mail and the services linked to it, as well as activating two-step verification. He also suggests using different emails for different purposes. For example, the work email should be different from the one you are using for your social media accounts or the email that is registered for an e-wallet or credit card accounts. A little precaution can minimize scams that might leak your data to an evil party.


