Editor’s note:
Cybersecurity is increasingly a problem that troubles you and me.
Data breaches, hacked cameras, email/telephone scams… Worrying news hit the headlines every now and then.
In this data-driven world, companies are so craving to know who you are, with industries from finance to healthcare and from advertising to e-commerce thirsting for data more than any time before.
We hope for a better world where technologies are so advanced to eliminate illness and bring about endless prosperity, but be prudent before we get there. Driven by the huge demand, data breaches are happening every now and then. The outside world may have already known everything about you.
This is the Part 2 of a 5 Part-Series. Link to the Part 1, Part 3, Part 4 and Part 5.
Data breach
We have witnessed the massive data theft repeatedly.
Sometime between May and July of 2017, a group of organized attackers hacked the server of the U.S. credit reporting agency Equifax and gained access to the personal data of 143 million users. The hacking put at risk information including names, dates of birth, phone numbers, addresses and social security numbers of 44% of the U.S. population, and exposed credit card numbers for around 210,000 Americans as well as the numbers of some driver’s licenses and dispute documents.
Equifax now faces a class action lawsuit that could cost it USD 70 billion for failing to protect users’ data.
Similar things happened in China as well. Towards the end of 2016, a 12GB data file containing the information of 10 million JD.com users was offered for sale on the black market. A source familiar with the matter said that the data file included such information as usernames, passwords, emails, ID cards, phone numbers and QQ accounts (a popular instant messaging app by Tencent), and had changed hands more than 100 hundred times in the black market for between 100,000 yuan and 700,000 yuan (approx. USD 15,800—USD 110,621).
Inside Job

External attacks are not the only cause for data breaches. Information is leaked from within the company as well.
In June 2017, 22 employees of Apple and its partners in China were arrested for infringing personal privacy by using their access to the company’s internal computer system to gather users’ names, phone numbers, Apple IDs, and other data and selling them on the black market for between 10 yuan and 180 yuan each (approx. USD 1.56 to USD 28.17).
Since an Apple employee ID gives one access to the company’s user database, hackers are offering Apple employees up to €20,000 for their login information, according to Business Insider.
In March 2017, JD.com broke the news that a network engineer named Zheng Haipeng who is in his probationary period at the company conspired with hackers and stole massive data on logistics, transaction and user identities. Police later found that it was not the first time the man acted as a mole. He had worked for multiple internet firms before and grabbed as many as 5 billion data entries in total.
The practice of trading personal data is far more pervasive than one can imagine. Among the cases made public, the online travel agency Ctrip, the courier company YTO Express, the online dating website Jiayuan.com, the e-commerce platform DangDang.com and the hotel operator Homeinns were all once targets of data theft.
Large internet companies are just data libraries in the eyes of hackers. Stealing and peddling personal data has developed into a full-fledged industry.
“There are only two kinds of websites in the world: those that have been hacked and those that are yet unaware that they’ve been hacked,” the network security engineer Wei Cong said to KrASIA.
Deep web & Hacker
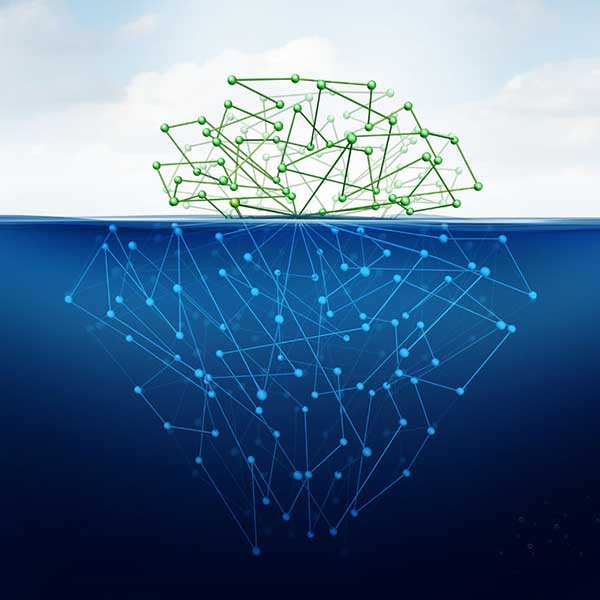
The ongoing illegal data transactions on the deep web are a known fact among insiders like Wei. On the 70,000 or so websites hosted on the hidden web, one can buy, in packages, personal information including ID numbers, social security numbers, phone numbers and addresses for different prices depending on how detailed the information is, along with all sorts of off-limit items like firearms, porn, and murder instructions.
Since data can be easily replicated, they tend to be sold and resold repeatedly once they enter the deep web and often end up surfacing in online forums or cloud storage platforms that are accessible to the general public. The value of the data decreases in the process. A data file that contains the personal information of 100 individuals could be sold for 1,000 yuan (approx. USD 156.51) on the deep web at the beginning, but the price may plunge to only 100 yuan (approx. USD 15.65) after several rounds of transactions.
For attackers with top hacking skills, stealing the personal data of hundreds of thousands of individuals is a piece of cake. Working in groups, top hackers throw hacking software into the internet randomly, which automatically hacks whatever websites it runs into. Such operation may give them unauthorized access to hundreds and thousands of websites at a time. The data stolen are decoded and processed and then sold to different buyers at different prices by dedicated salespeople.
Websites get hacked every second of every day.
