Privacy issues concern almost everyone in this internet era. When it comes to smart cars, technological breakthroughs are needed for automakers to produce safe automobiles both in terms of operation and information.
Many people raised doubts about data security after the emerging car manufacturer Byton (拜腾) debuted its new product Byton Concept. At a recent auto show, 36Kr, China’s biztech media and KrASIA’s parent company, had an interview with Abe Chen, the senior director of cloud technology, internet of vehicles and data security at Byton, on data security and related topics. Abe Chen had previously served at Tesla and Apple Inc., and led a team that won the 2017 WCTF.
He told 36Kr that Byton established a data security center at a very early stage to research and develop solutions to prevent and respond to hacker attacks, with the hope of applying the results to its first mass-produced car model. Byton also united with third-party partners to conduct data security tests to further improve the security performance of its products.
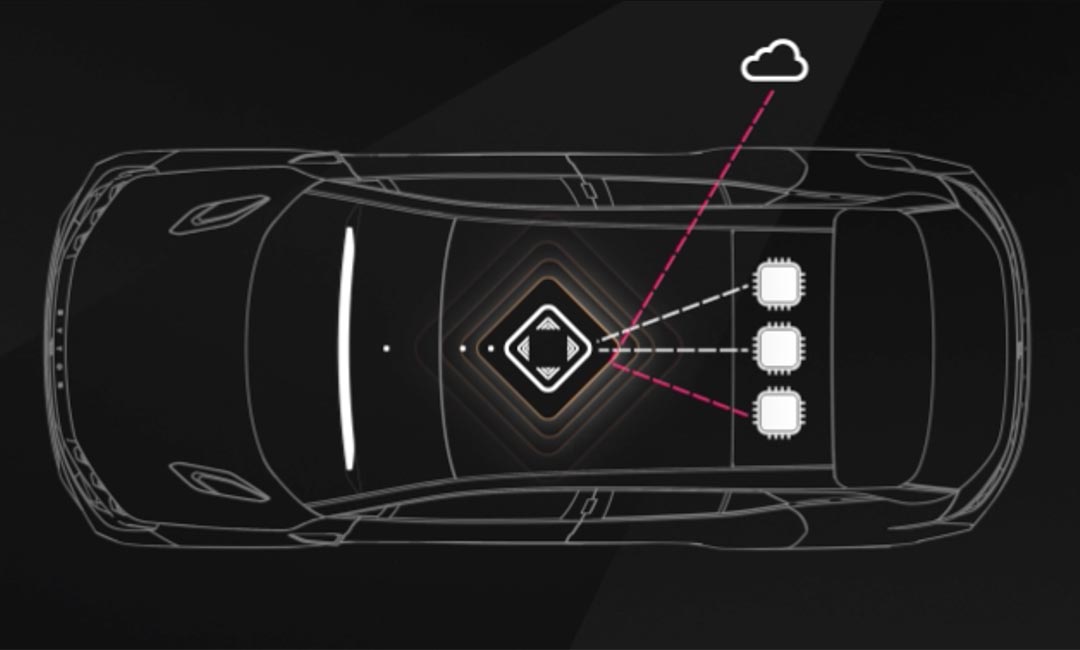
Abe Chen noted that intelligent gateways, with the ability to learn, are a core technology in Byton’s data security system. They can track car conditions in real time, efficiently identify potential faults and threats and take measures accordingly. The intelligent security cloud of Byton leverages strong cryptography to protect data and develops data models to identify malicious attacks.
“Byton has optimized the V2X technology to make car-to-car and car-to-cloud communications quicker and safer. Through Byton’s own mesh networking technology, vehicles can communicate with each other even when they are not connected to the internet. It’s expected to become a critical underlying technology for autonomous driving in the future.”
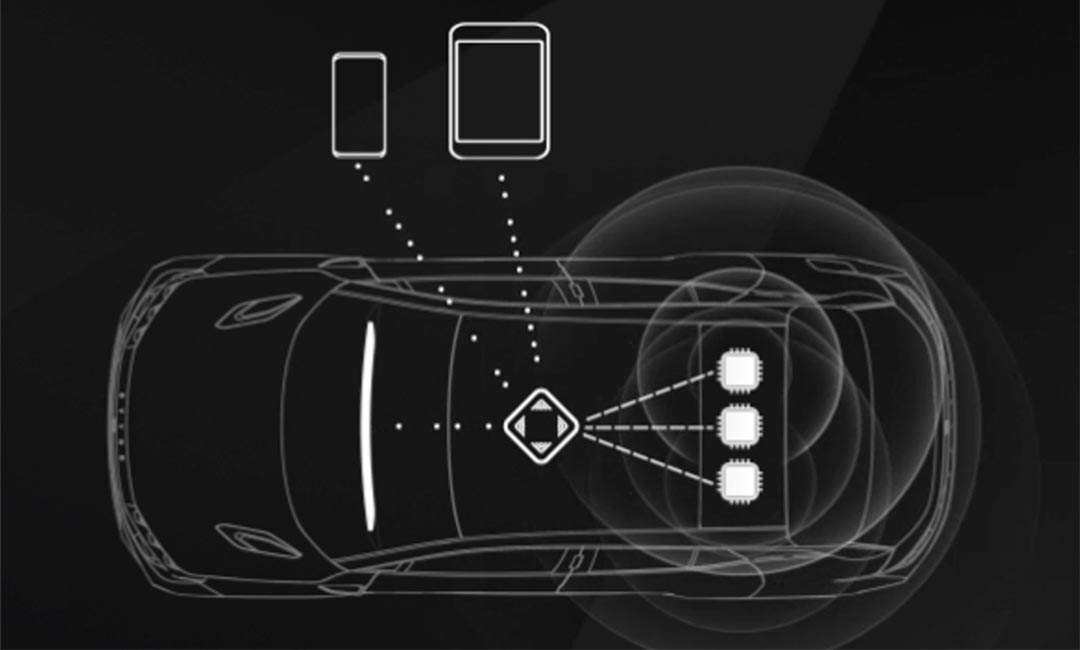
Each Byton user will have an account of his own, which can be used on his phone, for his car as well as on the cloud. “Even if hackers operate inside Byton’s cars, users’ account information and personal data can be protected as they are encrypted and stored safely in hardware. Byton pledges to explain in detail to users concerning how internet applications will affect their privacy along with the launch of the car model. Users will be given the right to choose what data they want to share, for how long the data is to be stored, when it should be deleted, and how it should be handled.”
Here is an excerpt of the interview between Abe Chen and KrASIA’s parent company 36Kr.
Q: We know that you had your own team in the U.S. Did you join Byton by yourself or with your team?
A: All my team members joined Byton. At present, there are 6 people in the Data Security Center, and we hope to recruit more.
Q: You mentioned that each user of Byton will have an independent ID, but a car may be used by more than one person. Can those who don’t know how to operate the car, for example, the elderly of the family, start the vehicle without logging in?
A: The car is incorporated with facial recognition technology and is therefore able to recognize whether the person behind the wheel is the father, child or grandparent. You don’t have to log in every time to use the car, but some functions can be activated only with an ID. Suppose your friend borrows your car and he doesn’t have an ID. The car will know that it’s a stranger sitting in the car and will let you know that your car is being used by someone. If your friend wants Byton to recognize him and know his personal preferences, and be able to drive the car, he’ll have to create his own account.
Q: Passengers’ information is stored in the cloud. How does Byton guarantee password and data security?
A: Some information has to be stored in the cloud, but some doesn’t.We are also exploring other methods to allow people to create safer IDs, and we will keep the public up to date on our progress. In fact, Byton does not access users’ data, which are encrypted in the system. We will make sure that users know which parts of their data are being stored and have the right to determine whether to delete the data.
Meanwhile, we have security modules for hardware which are kept in the Data Security Center. We use a mixed approach to data storage, storing only the less sensitive information in the cloud and the more sensitive data in our Data Security Center.
Q: You mentioned security modules for hardware. How does Byton prevent hacker break-ins when it comes to software? Do you use data encryption techniques or firewalls? Are there any data breach prevention techniques that we don’t know?
A: One is machine learning. The traffic data consumed by a car can often be predicted and a pattern can be found. We may, therefore, establish a model to detect abnormal conditions. To develop such a model, we must collect data from numerous cars to train the model to tell normal conditions from abnormal ones. The most important method to ensuring software security is conducting tests. We have a dedicated break-in prevention team whose job is conducting endless tests on our products to ensure that relevant response mechanisms are put in place in the process of software development.
Q: iPhones can be unlocked through jailbreaks. That means Apple IDs are not completely invasion-proof. Is it even more difficult to prevent such things when it comes to vehicles?
A: I think it is often when more functions are addedo to a product that security is compromised. If security is traded for functions, cars will certainly be less secure. We set up a data security center instead of an internet of vehicles center because we believe safety is more important than vehicle connections. Unlike other manufacturers, which have engineers develop products first before integrating security technology, we ensure safety first before considering vehicle connections. This is an issue of priorities.
Q: What do you think is the worst thing about an open system?
A: The worst thing about open systems is that too much power is given to third parties. We will use APIs to reduce third parties’ control of content. We need to make sure that third parties are standards-compliant. For instance, when it comes to autonomous driving, we have control over relevant data most of the time. We must make sure that we are in charge and relevant systems meet our standards or are under close scrutiny by us.
Q: How open are Byton’s products to third parties? If you work with a third-party, how do you ensure that you have control over the services offered?
A: Byton’s intelligent gateway will take the necessary safety measures, whether the services are provided by us or a third party. It will detect when unsecure content is being entered into, say, the car’s voice system, screen, or information and entertainment system and advise users to stop.
Q: Will Byton cooperate with third-party security researchers?
A: We engage in security studies ourselves, and we would like to cooperate with researchers from third parties. My team participated in a hacking competition previously. We also gave lectures at many universities and conferences on security, hoping to spread knowledge on how to make cars immune to intrusion. I also hope that we can host our own car hacking contest one day.
Q: Regarding your relationship with governments, do governments have the authority to use your data? Under what circumstances will infrastructure networks have access to your data? Have you had any talks on relevant issues with the U.S. or Chinese government?
A: We must act in accordance with local regulations if we want to operate in a country. We may share our data if it’s required by law. However, if it’s not, we have the right to say no. This is how we act, including in the U.S. Only in this way can we better protect the privacy of users. We will store users’ data locally. The data of European users will be stored in our data center in Europe; the data of Chinese users in our Chinese data center and those of U.S. users in our U.S. data center.
Writer: LIU Shiwu
